Category
OpenClaw Security Risks: How to Deploy Agents Safely

Last updated: May 2026
Installing OpenClaw is easy. Securing it for mid-market business operations is hard. We see operators rushing to deploy AI agents to automate workflows, but unmanaged, open-source deployments introduce severe vulnerabilities to your infrastructure. If you do not govern your AI workforce, you are exposing your company's operational truth to the public internet.
- Data Leakage: Default setups often route proprietary data through public LLM APIs, exposing your intellectual property.
- Browser Relays: Unrestricted agent access to web portals can lead to destructive actions if the agent hallucinates.
- Missing Access Controls: Without isolated Workspaces, an HR agent might access sensitive financial directories.
- The Solution: Deploy OpenClaw on dedicated on-premise hardware with strict human-in-the-loop approval gates.
The Reality of Shadow AI Agents
Mid-market CEOs often worry about hackers breaching their firewalls, but the most pressing threat today is internal. Your employees are likely downloading open-source agent frameworks and running them locally. This creates a massive problem known as shadow AI.
When a team member uses a localized agent to parse an internal spreadsheet, that agent needs a language model to process the information. If the agent connects to a public API endpoint, your proprietary data, margins, and client details are sent outside your secure network. You lose control immediately. Securing your infrastructure means transitioning from scattered shadow AI to a centrally managed OpenClaw setup.
4 Critical OpenClaw Security Risks You Must Manage
A basic installation of OpenClaw provides the engine for automation, but it lacks the enterprise guardrails necessary for safe operation. You must actively manage these four critical risks.
1. Public API Data Leakage
The core function of an AI agent is to read, analyse, and act on data. If your OpenClaw Node relies on public cloud models to process requests, you are creating a direct pipeline for data leakage. Every invoice, employee record, and strategic document processed by the agent becomes part of an external data stream. Securing this requires configuring your node to utilize locally hosted, private models where the data never leaves the building.
2. Unrestricted Browser Control Relays
Agents execute tasks on the web using Browser Control Relays. These relays allow the AI to click buttons, scrape data, and submit forms inside your SaaS applications. If an agent is not restricted by strict URL allowlists, a hallucination could cause it to delete records or alter configurations in your CRM. Browser relays must operate in heavily constrained environments with predefined execution pathways.
3. Flat Permissions and Missing RBAC
A digital employee needs boundaries just like a human employee. In a default open-source deployment, permissions are often flat. This means an agent designed to draft marketing emails could theoretically access your accounts payable directory. To prevent this, you must implement strict Role-Based Access Control (RBAC). OpenClaw Workspaces must be configured as isolated data silos, ensuring an agent only has the context and access required for its specific role.
4. Execution Without Human Approval
The allure of AI is total automation, but fully autonomous execution in business operations is dangerous. An agent acting without oversight can send incorrect invoices to clients or approve invalid expenses. The most vital security measure is the human-in-the-loop gate. High-risk write actions must pause and wait for a human manager to review the agent's work and click a final approval button.
Bring Your AI In-House.
Your employees are already using AI; you just don't control the data. Book a Free AI Assessment to map your shadow AI exposure and get a step-by-step plan to deploy a secure, private AI workforce on your own infrastructure.
How to Secure Your OpenClaw Deployment
The solution to these security risks is architectural. You must build a secure environment before you deploy your first agent. This starts with the hardware. By running the OpenClaw Node on dedicated on-premise servers or a secure Virtual Private Cloud (VPC), you establish an impenetrable perimeter.
Next, you must configure isolated Workspaces for every department. This acts as an internal defence system, containing any potential errors within a specific operational silo. Finally, you implement comprehensive audit logging. Every tool call, web click, and file accessed by an agent must be recorded. If an error occurs, your IT team must be able to trace the exact decision path the agent took.
Governance is the Hardest Part of Private AI
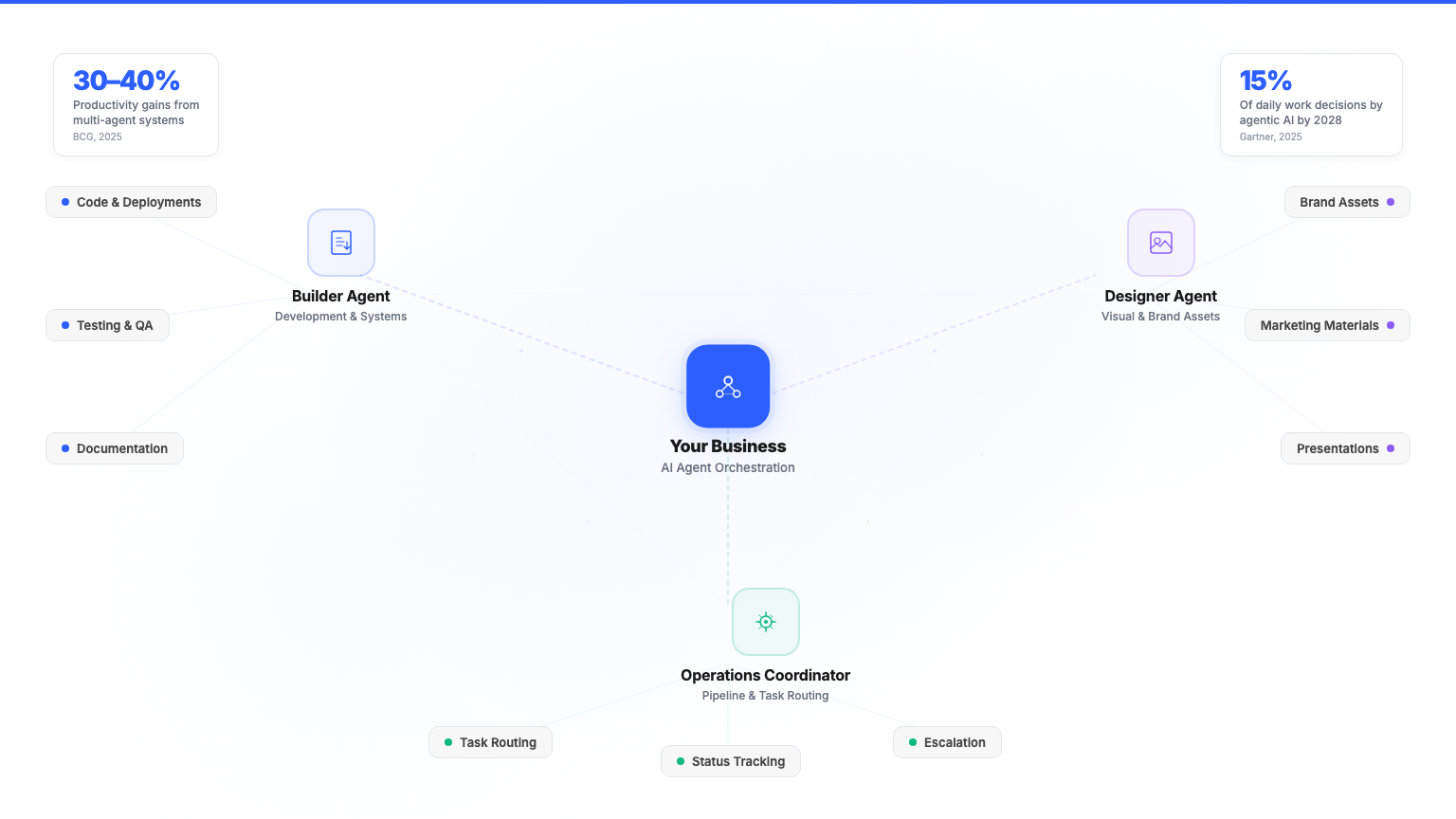
Getting the software to run is the easiest phase of building a private AI workforce. Governance is where deployments succeed or fail. Your company needs visible approval logic, rigid data boundaries, and clear escalation paths for when agents encounter unknown variables.
This is exactly what we map during our free AI Assessment. We look at which processes are costing you the most, and we design the secure architecture required to let AI handle them safely. You are not just deploying code; you are managing digital employees. They require oversight, structure, and security to operate effectively.
Bring Your AI In-House.
Your employees are already using AI; you just don't control the data. Book a Free AI Assessment to map your shadow AI exposure and get a step-by-step plan to deploy a secure, private AI workforce on your own infrastructure.
Frequently Asked Questions
What are the main security risks of OpenClaw?
The primary risks involve data leakage through public API endpoints, destructive actions executed by unrestricted browser relays, and unauthorized data access due to poor workspace segmentation and flat permissions.
Can OpenClaw run without an internet connection?
Yes. When configured correctly on private infrastructure, OpenClaw can operate completely offline using localized language models, ensuring total data sovereignty for your business.
How do you stop AI agents from leaking company data?
Data leakage is prevented by isolating the OpenClaw Node on dedicated hardware, utilizing local LLMs instead of public cloud APIs, and enforcing strict Role-Based Access Control within isolated Workspaces.
Why do AI agents need human approval gates?
Human approval gates act as a critical fail-safe. While an agent can autonomously process 99 percent of a task, a human manager must verify and approve high-risk actions, such as sending external communications or altering financial records, to prevent costly errors.
Ready to Own Your AI?
Apply for the free AI Assessment. In 60 minutes you walk away with a 12-month plan tailored to your business. No software demo. No obligation.
Free Planning Session →